
After you’ve designed and simulated an entanglement-based quantum network, it’s tempting to begin building the full-scale deployment. However, building a pilot quantum network to test the real-world compatibility of your selected hardware and software and benchmark the performance of your planned full-scale deployment on a smaller scale can save a lot of time, money, and give you a better foundation for deploying a full-scale quantum network.
Pilot network requirements: hardware, software, and experience
Building a pilot quantum network is where the process of Design and Emulation informs the building of a physical quantum network. There are specific hardware, software, and experience requirements at this stage. Being aware of these requirements will ensure your pilot quantum network is informing the implementation of the intended full-scale deployment.
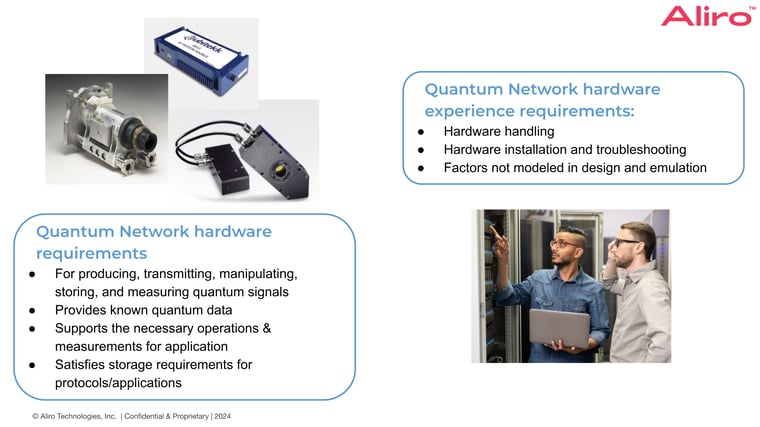
At a high level, the hardware needed to implement the pilot quantum must be capable of producing, transmitting, manipulating, and measuring quantum data in the form of qubits. Some networks will also need the ability to store quantum data, in order for a message to cross the network before it can be used. For quantum networks, much of this hardware will be geared towards qubits in the form of photons, particles of light.
Qubits are very sensitive to external noise. There's a notion of quality of quantum data, which is referred to as fidelity, and higher fidelity means higher quality data. The hardware used in the pilot quantum network must not reduce the quality of the quantum data too much, or the network will not be usable.
Additional hardware requirements that should have been investigated during the Design and Emulation phase include that the selected hardware produces known quantum data: it supports the necessary operations and measurements needed to implement the desired algorithms and applications. For example, if the pilot network is using a photon source for generating entangled pairs of photons, then it is necessary to know the specific kind of entanglement that the photons will be carrying. Otherwise, the network will not be able to competently claim what kind of quantum information is being distributed between the nodes in the network. This is necessary, as many algorithms and protocols depend on identifying the kind of quantum data being processed in order to work properly. Once the kind of quantum information is identified, the hardware components can be used to manipulate this data and extract the information using measurements. Selected hardware must also satisfy any storage requirements for the protocols and applications used in the network. Since classical messages will be exchanged as part of the applications and protocols, it will be necessary to faithfully store this data for the duration of message exchange.
Aside from these kinds of requirements, which are more oriented towards the primary quantum devices that realize the network, there are also classical hardware requirements that need to be met. As mentioned previously, we need the ability to send classical messages between nodes in the network, so classical networking infrastructure will be needed in addition to quantum hardware. The network needs to enable classical communication between the relevant nodes in the quantum network and should observe low latency to respect the storage constraints imposed by our quantum hardware.
Auxiliary hardware components which were not modeled in Design and Emulation might be required, too. Hardware vendors can provide input and recommendations for supplementary components that will allow the hardware to operate as expected, or even further improve its performance. These recommendations are especially helpful when an organization does not have intimate experience with the hardware internally.
It is also important to ensure the selected hardware is compatible with software used to configure and control the quantum network. Oftentimes, hardware components will be packaged with software like graphical user interfaces, which are helpful for running experiments in a lab, but do not provide automated control and configuration of the hardware. It is not practical to have network operators using graphical interfaces for real-time control of individual components in the network.
In conjunction with the hardware itself, experienced individuals capable of deploying the hardware will be necessary. Specialized experience with handling and transportation of sensitive components is critical for moving equipment between physical locations without damaging it or altering its behavior. Mishandling equipment can be an expensive mistake. For example, if the pilot quantum network is utilizing sensitive optical components, it is important to shield these components from bright light that could damage them. Specialized experience in installation and troubleshooting of the various hardware components is also crucial to the success of the pilot network. Hardware components need to be connected to one another correctly to ensure devices operate as expected. Experienced individuals can easily identify when such connections have been made incorrectly, saving time and money as the pilot network grows.
Experience with environmental factors that may not have been modeled in Design and Emulation is also critical. These factors can include external sources of noise, like mechanical vibrations or stray electromagnetic fields, that are specific to the location you want to deploy the pilot network. The hardware deployment must ensure that such external factors are accounted for and that their effect on the devices is reduced so performance of the pilot network closely aligns with what is anticipated from Design and Emulation. A network may need electromagnetic shielding or vibrational damping at sites where the hardware is being deployed.
The key to success in all of these cases will be collaboration with hardware vendors. Vendors know their equipment best, and establishing good communication habits with them will greatly benefit your own deployments. Vendors can provide hardware documentation, knowledge of best practices, and possibly training to help build the internal familiarity and experience that will be necessary for long term support of the network.

Several different software components will also be needed to build a working pilot quantum network:
- Software that controls the hardware components that make up the quantum network
- Software that executes the desired network protocols.
- Software for control and orchestration of the network.
- Application software, which makes use of the services provided by the network in order to perform higher level algorithms or tasks.
This software will likely be bundled together in the form of a network operating system that runs close to the hardware and is the main driving logic for exchanging quantum data over the network.
In addition to exchanging quantum data, it will also be necessary to manage, configure, and monitor the network. With control and orchestration software, administrative tasks like reconfiguring devices or keeping track of the status of network nodes becomes much easier. This software isn't completely necessary during the Pilot and Trial stage, since the pilot should be handling only a few network nodes. However, once the pilot quantum network grows and eventually scales to full deployment, this type of software will be absolutely necessary, as it will be impractical to manage network nodes by remotely connecting to each individual node.
The network operating system, control, and orchestration might take care of things like transmitting quantum data across the network, or creating resources like entanglement that can be used by the application, but the application software actually uses these services to implement desired use cases like quantum secure communications, or distributed quantum computing.
The network operating system and application software components must run quickly enough to respect timing constraints of the selected hardware. This includes any timing and synchronization as well as limited storage times of quantum data. At present, many hardware devices that support the storage of quantum data can only do so for brief amounts of time - on the order of microseconds, or milliseconds. In order to make use of the quantum information that gets stored in these devices, decisions need to be made very quickly about how to use stored data. Many factors influence the timeliness of software, such as its implementation and the computing platform it is executed on, so careful attention must be paid to this element of the pilot quantum network.
All of the various software components in the pilot quantum network need to be informative and provide actionable information in the case that failures occur. Analytics can help judge performance metrics such as data transmission rates or data fidelity, while logs can provide timestamped records of events that caused these metrics to drop. Both analytics and logs are invaluable for monitoring the network and for communicating any software or hardware issues to vendors.
As with hardware, there is a need for experience when dealing with the software components of your pilot network. For instance, it is important to have individuals that are capable of installing and troubleshooting the software assisting with the pilot quantum network. These individuals need to know how the software should be deployed and how common errors can be avoided and resolved. For example, if for some reason network nodes are unable to communicate with each other over the classical network, or if network nodes begin to behave unpredictably, experienced individuals will be able to identify when these situations are occurring and react quickly.
Individuals that have experience with operational security will also be key to the success of the quantum network. Many security oriented applications for quantum networking, like Quantum Secure Communications, have assumptions on the classical communication infrastructure in order to meet their security guarantees. Even below the application, at the protocol level, it is also necessary to employ techniques like authentication to prevent any unauthorized actors from attacking the network and preventing it from servicing its users.
Experience with troubleshooting the network protocols themselves is also helpful. During the testing of the pilot network, it could be the case that the protocols are not acting correctly, and it will be necessary to have individuals knowledgeable of the protocol behavior identify the specific errors that are occurring. Just like with hardware, good communication with software vendors will provide additional support such as providing documentation and training in the software platform when rolling out a pilot network.
What makes a “good” pilot quantum network
A “good” pilot network is built using a well-defined process and meets specific hardware / software / experience requirements that will ensure you are building a pilot network that will provide the best feedback possible on the planned full-scale quantum network. The design goal of the pilot quantum network is to validate discoveries made during the Design and Emulation phase, as well as get an idea for the expected behavior of the full-scale network.
To accomplish this, the pilot quantum network should be informative of the performance of the hardware and the behavior of the software that's controlling it. This can be accomplished in 2 ways: building a pilot network that is reflective of the least performant aspects of the full-scale network OR building a portion of the proposed quantum network.

Designing a pilot network that's reflective of the least performant aspect of the proposed full-scale network
The biggest influences on network performance include the distances between the network nodes, the number of hops to traverse between network nodes, as well as the hardware components themselves. Building a pilot network that reflects the worst case scenario of such influencing factors in the proposed full-scale network will help to ensure the entire network is capable of fulfilling the intended applications.
As mentioned previously, quantum data has a notion of quality known as fidelity. Fidelity is one of the most important metrics to evaluate at this stage of building a quantum and is heavily influenced by all of these properties of the network: the distances between the network nodes, the number of hops to traverse between network nodes, and the hardware components themselves. To ensure that the fidelity of quantum data in the proposed full-scale quantum network can be properly gauged, the pilot network should be built to capture these least performant aspects of the full-scale network.
Designing a pilot network that is a portion of the proposed full-scale network
With a limited amount of hardware available to implement the network, one might consider deploying a portion of the full-scale network for the purposes of a pilot network. A benefit to this approach is that progress is being made towards the full-scale quantum deployment. However, it is imperative to be aware of whether or not that portion that we want to deploy is actually reflective of these least performant aspects. If it is not, there is a risk that those worse performing portions of the proposed full-scale network might not satisfy the network requirements. The results from the pilot network in this case will need to be assessed in regard to whether or not those least-performant portions of the full-scale network will be sound.
Examples of pilot quantum network designs and considerations can be found in the on-demand webinar, Pilot and Trial: the 2nd Stage of Implementing Quantum Networks.
From pilot quantum network to full-scale quantum network
An organization is ready to move onto building a full-scale network once it has determined that the pilot network performance is satisfactory. The pilot network needs to have been tested, verified, and it has to meet the standards for growing into full-scale quantum network deployment.
Testing the pilot network may uncover some other details about the behavior of the network, such as whether or not an application can be executed on a particular set of nodes or whether it is possible to transmit quantum data between a given set of nodes. As the network grows in size and scope, it will need to be more thoroughly tested to verify the behavior and performance of any new hardware components that were deployed.
A thorough plan for scaling the pilot network to the full-scale network will include proposals for procuring additional hardware and software necessary to deploy the full-scale network, a layout and deployment strategy for the full-scale network, as well as testing and verification plans for benchmarking the network as it grows. Scaling up to the full-scale quantum network can be a multistage process where additional links and network nodes are gradually added onto a base network. At every stage of scaling up, a similar set of tests that were done initially on the pilot network will be performed, using the knowledge and experience developed through building the pilot quantum to verify progress towards the full-scale quantum network deployment.
Building a pilot network is the first step in transitioning from a network design to a full-scale deployment. It provides a means to verify the plans for a full-scale network, and it gives organizations a head start on developing the necessary experience for supporting the full-scale network once it is built. Communication with hardware and software vendors will be critical for deploying a quantum network. An organization is not on their own when building an entanglement-based quantum network, and establishing good communication channels with the providers of network hardware and software will ensure that the right hardware and software is being selected to fulfill the network’s requirements. Thorough testing of all the pieces that make up the pilot quantum network is key to the success of a full-scale quantum network deployment. Having testing plans for everything from the smallest hardware components to the entire pilot network will ensure issues are caught early on and provide confidence that the network will meet the standards required for specific applications. By building a pilot quantum network, an organization can stay agile throughout the entire process of expanding to full-scale quantum network deployment.

